Yet Another Work From Home List
If you keep up with Corporate Armor on social media, YouTube, or our blogs, you’ve probably noticed we have been posting a lot about the influx of telework, and new working from home standards. We want to make sure our customers have all the information they need to make a smooth transition to remote work. So why not post another list? This time we are taking a slightly different approach though. This time we are going to outline 11 ways you can protect and secure your company’s assets within a few days. Plus, 3 bonus steps that will ensure long-term protection of your company’s data and equipment.
Protect Your Access
1. Make sure that users are set up properly with access to the correct systems and information. This can be done easily and efficiently using Active Directory (AD). Not only can this help ensure that users can access what they need to do their jobs, but it can also prevent unnecessary access to sensitive company data by the wrong person.
2. Enable an additional layer of access protection. User validation can be ensured in this case by using multi-factor authentication (usually two-factor), which is now supported by almost all modern IT systems. This helps to authenticate users using SMS, physical token, email, or generated numeric codes e.g. in the mobile application. Now that users will be accessing company information from unsecure locations, multi-factor authentication ensures that only your employees can access your data.
Remote Connection Into Your Network
3. Ideally an active Virtual Private Network (VPN) should be deployed. This way, connecting the computers to your network and to sensitive systems, data, and storages is always facilitated using a VPN
Protecting Your Workstations
4. Any computer that may have company data stored on it, should be encrypted.
5. Among your working equipment, laptops are a quite common category bringing especially high risks.
- Encrypt hard disks before submitting to the user to protect the workstation from data leakage in the event of device loss or theft.
- Separate user working profiles from others, such as home users, to prevent unwanted access by unauthorized users; the profiles can be separated both at the operating system level and in web browsers.
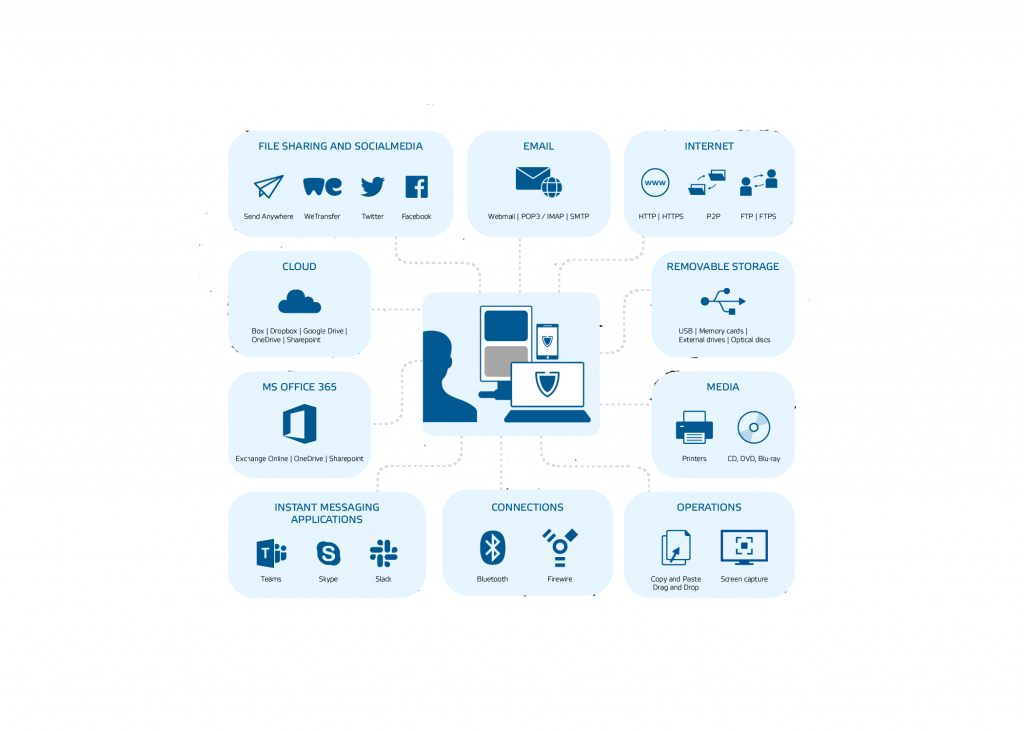
- Home or third-party external storage media are also often attached to the portable notebooks, which increases the risk of passing malware and opens doors for theft of sensitive data. This can be controlled using Device Control solutions.
SECURING YOUR ASSETS WITHIN A FEW DAYS
Now a few more actions, which can lead to a more secure company environment, even in the case of telework.
Portable Devices
6. Portable storage media such as USB keychains, external hard drives or mobile devices are als a frequent source of leaking sensitive information, company know-how, etc. Encrypting external media and hard drives, either by a physical or virtual method, is certainly highly recommended.
Secure Perimeter
7. Introducing a safe working perimeter significantly reduces the risk of leaking sensitive information. Also restricting available services helps greatly to protect data and data transfers:
- Using public freemail clients and web-based email services (yahoo.com or gmail.com) entails considerable risks when communicating from a workstation.
- The same applies to using well-known public file storage or freely available cloud services (e.g. Dropbox, WeTransfer, etc.).
- Generally, restrict the use of external devices and their connection to the workstation.
Quick User Education
8. Explaining the current situation to the users. Update security policies. Share a few highly effective security tips – these are all steps that will help to secure users working from home. Issuing recommendations focused on working with sensitive data and on working with IT tools and systems.
9. Maintain your work routine, working hours, and calendar. Working from home does not mean freelancing. Work ethics, along with frequent contacts, are also important elements in keeping reasonable and safe behavior.
Remote Access
10. High risks in terms of data security are also associated with remote access. Remote Access allows users to connect from his or her home computer to their work computer, further accessing internal systems and sensitive data. From the IT administrator’s point of view, this is a big challenge, and a DLP solution may help with mitigation.
11. The IT administrators should have available tools for monitoring risk factors and security incidents, ideally with the option to send instant security alerts and/or regular reports on your most important data.
LONG-TERM PROTECTION OF YOUR COMPANY DATA & EQUIPMENT
There are also long-term projects that take some time, but that lead to an ideal protection of your internal IT environment. Prevent a similar situation in the future – be prepared!
Deploying Active Data Protection
12. Based on our experiences, we recommend the IT administrators to differentiate between official working hours and non-working hours of their users, and to monitor their activities and security incidents outside working hours. Security incidents, attempts to leak sensitive data, and unauthorized access to internal systems often happen after hours.
13. Enhance your data security and user experience using DLP (Data Loss Prevention) solutions.
Detailed User Training
14. Your company network can be only as secure as the network of users connecting to it; educate your users about the best practices for setting up their personal computers, devices, and networks:
- Antivirus software and their settings
- Updating applications, operating system, and home network components
- Using third-party applications and downloading apps from Stores
- Setting WPA2 with a password protection for connecting to the home Wi-Fi
At Corporate Armor we have years of experience with remote work solutions. Our security experts are available to answer any questions you may have about preparing for remote work.
